404
Oops! This page no longer exists.
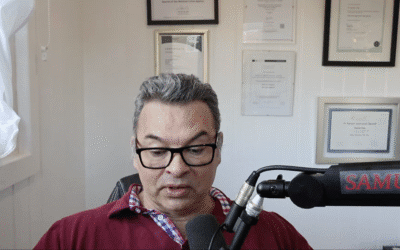
Not to be confused with our podcast, 404 Cybersecurity Not Found!
Latest episode:
Popular Services
Penetration Testing
Identifying vulnerabilities before they become issues
Our service simulates a simulated cyber attack designed to exploit the vulnerabilities of your network.
Vulnerability Assessments
Identifying risks and vulnerabilities
Our service identifies, quantifies, and prioritises the vulnerabilities in your cyber systems.
Cloud Assessments
Analyse your organisation’s cloud infrastructure
An evaluation of the potential risks associated with using a cloud-based system.
Get in touch
Let's find a solution
If you want to chat, give us a call: 0121 740 1304
Or, email us: [email protected]