Can we just start by saying we do enjoy using Zoom as an organisation, we find the features very useful and the ability to green screen backgrounds has really helped with team morale and appreciate how valuable these types of tools are at the present time
As the world has been forced to work from home by the Covid-19 pandemic, teleconferencing has seen a massive rise to keep organisations running. There are many providers of teleconferencing including tech giants such as Microsoft and relative newcomers to the segment like Zoom. At Samurai we use Zoom and host our morning team meeting using it. As an inquisitive bunch, on our call this morning we started to play with Zoom, testing its security and theorising possible attack scenarios. After a 30-minute scrum hack we had found several vulnerabilities in the platform which allowed us to find and join other meetings and bypass password authentication. We want to keep everyone safe during these interesting times so we have also developed a guide to protect against these attacks which is included in this blog.
Issue 1 – Meeting ID’s are brute forceable
Firstly we acknowledge this issue is not a new one, we did at first get excited until it was pointed out that it was originally raised by Checkpoint – https://research.checkpoint.com/2020/zoom-zoom-we-are-watching-you/ more information can be found in this blog by tripwire.
However, reiterating this point is needed as it’s a precursor to the issue we found further down.
The first issue we found in our half-hour of fun was how easy it is to find legitimate meeting numbers, which could then allow you to join the meeting if the host has not secured it properly. If you have a blank background when you join, enter your name as [space] ” ” and don’t mute the microphone (so the mute symbol isn’t visible) then other than a black square which is hidden on black background, you are invisible.
Zoom meetings utilise a 9, 10 or 11 digit number as the meeting number. To connect to the meeting you just need to go to https://zoom.us/j/123456789, where 123456789 is the meeting id. In the screenshot below you can see that we sent ten requests to random nine-digit numbers and found two legitimate meetings. These valid meetings are highlighted in orange and distinguished by their smaller response length.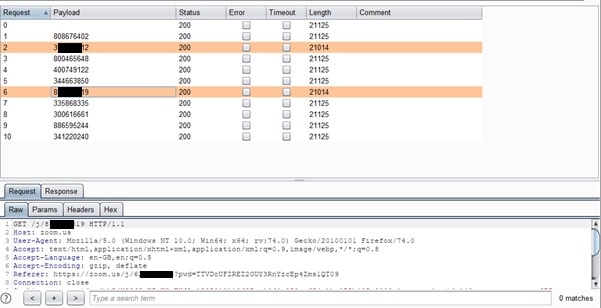
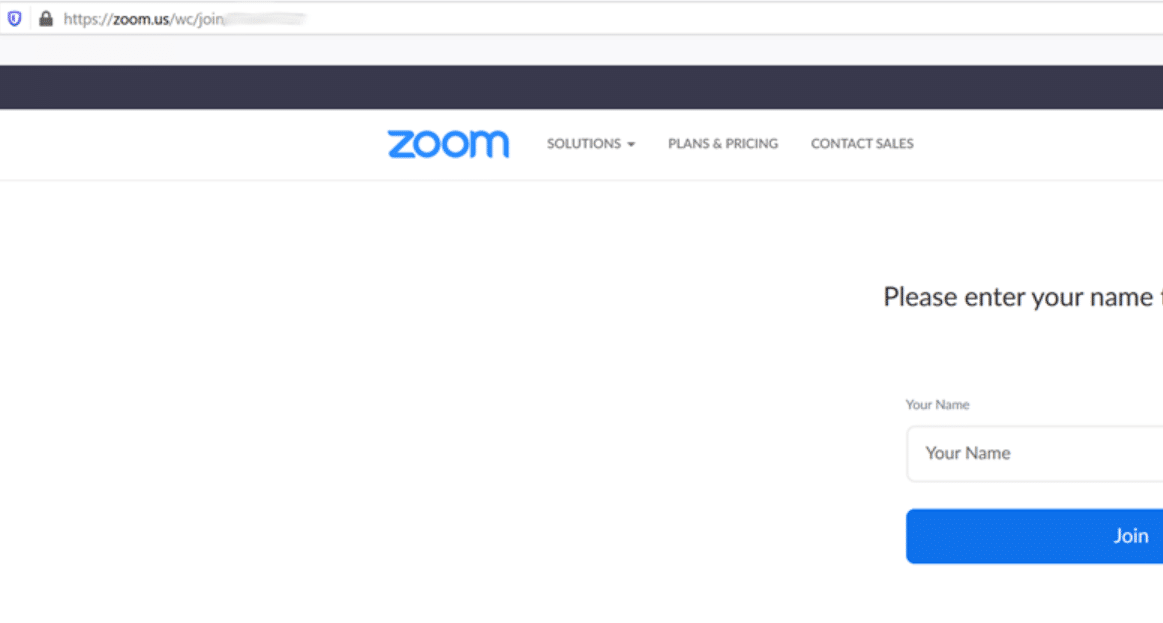
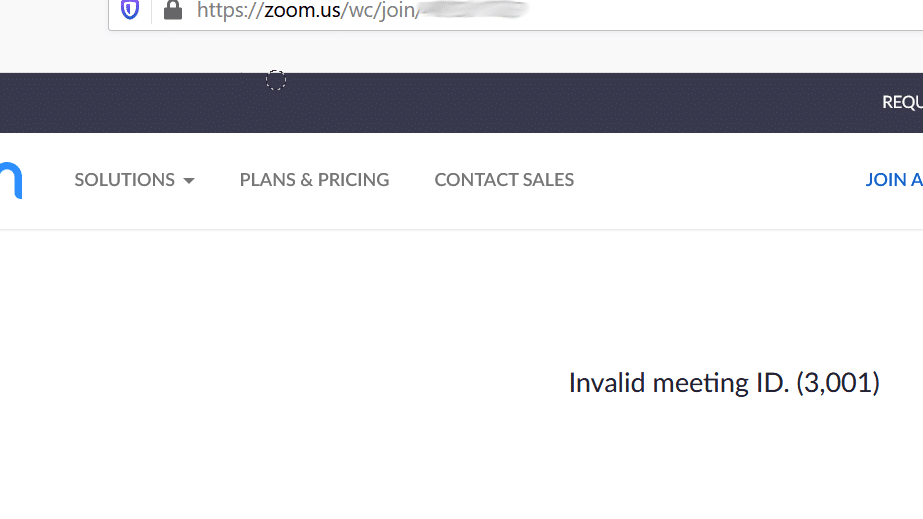
The above shows how it looks in Burp, however, in your browser here are some examples we found using brute force below: –
Solution–
To prevent people from exploiting this and joining your Zoom meetings you must set a password. When setting up a meeting this is the default option, however, from our very limited testing we found this is something that most weren’t doing. Even if you set the requirement for a password in your Zoom meeting this can be bypassed as we found this morning and discuss in the next section.
Issue 2
The default Zoom setup means you can bypass pin code/password by dialling in to meeting.
As part of our investigation we found that Zoom’s default settings do not require a pin code/password to dial into the meeting. Hence all a malicious user requires to access a meeting is the meeting ID. As we discussed above this is not difficult to obtain.
On our morning call (which we password protect) one of the team members was able to join the call without entering the pin code/password by dialling in via the Zoom phone number and not entering the pin number.
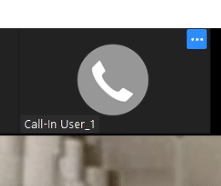
What was worse by dialling in with 141 at the start of the Zoom number they just appeared as Call-in User_1.
In large calls like this may go unnoticed.
We feel one of the main issues here will be many companies will have (for legitimate reasons) rushed into using Zoom, and will, therefore, have not spent the time needed to ensure the configuration has been secured.
Solution
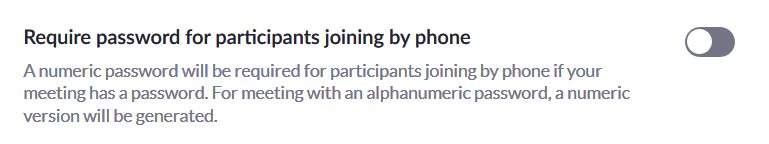
To help remove this issue we strongly recommend companies enforce the pin code/password for anyone joining by phone – invites contain this number by default so it shouldn’t cause too much trouble.
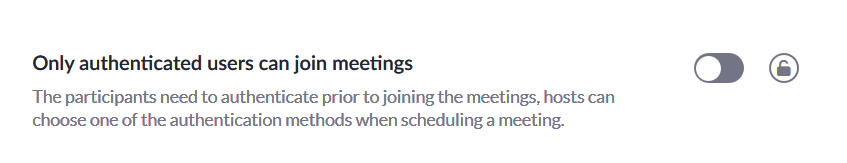
The option can be found in Zoom settings via the administrative panel.
https://zoom.us/account/setting/
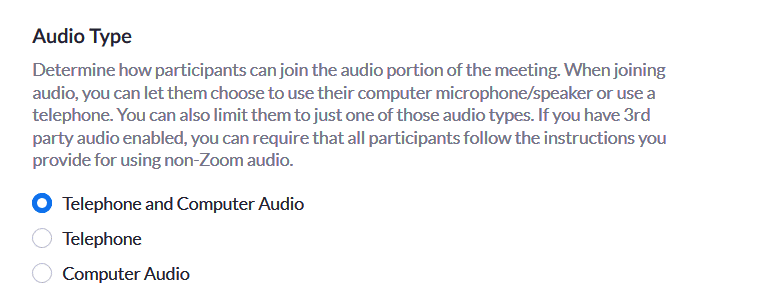
Additionally, you can disable the Telephone option altogether, but we recognise this may not be a preferable feature.
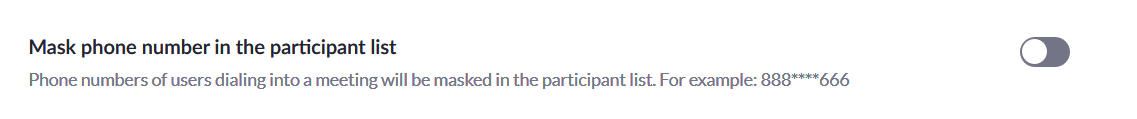
As mentioned above, if you dial in, your number is displayed, some users who use mobile phones might not want to share/display these (especially if they are personal numbers). They can dial in using 141, or the administrator can mask the number for all.
Issue 3
Another issue we found this morning in our hacking scrum was the ability to replace another users microphone input, giving you the ability to speak as if you were them. This builds on our finding that you could join from your phone without a password. In Zoom you can join using either the audio from your computer or telephone. If you join from your telephone you can just require the meeting ID and a password (if the host set this as a requirement).
Fix
To prevent this from happening you can either set a password for dialling in from a telephone, which would make the attack much harder or disable the ability to dial in.
Issue 4 – Default configuration for Zoom – How to harden the system.
As discussed throughout this blog – we feel a lot of the issues which exist could be fixed by reviewing the configuration settings of Zoom. Hence, Zoom has a lot of security features, they just need enabling.
A few examples of how we believe we can harden the system are given below:
Zoom presents two options to connect to a session.
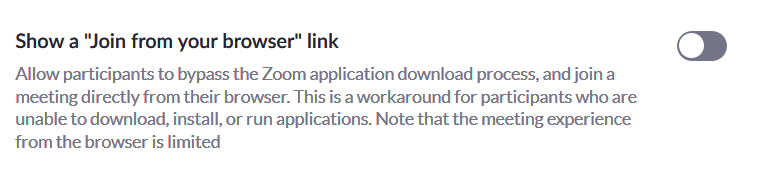
Either (Zoom’s preferred way) by downloading their .exe or via the web browser.
The .exe might
Unfortunately, Zoom only offers this option if the .exe fails.
There is a setting to allow “join from browser” when they click the invite link.
Solution –
2FA is a key feature, especially for administrative accounts. This option can also be enabled.
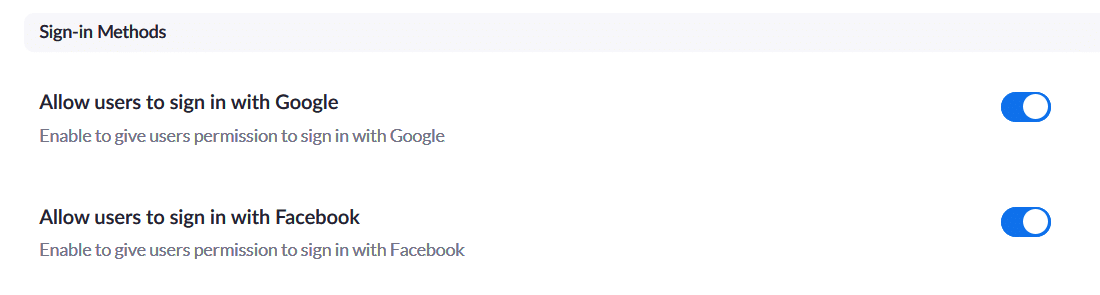
Another consideration would be – allowing people within your organisation to sign in with their personal Google or Facebook is normally a recipe for issues, as the lines between personal accounts and work accounts blur. It is recommended that these are turned off – unless the organisation uses GSuite.
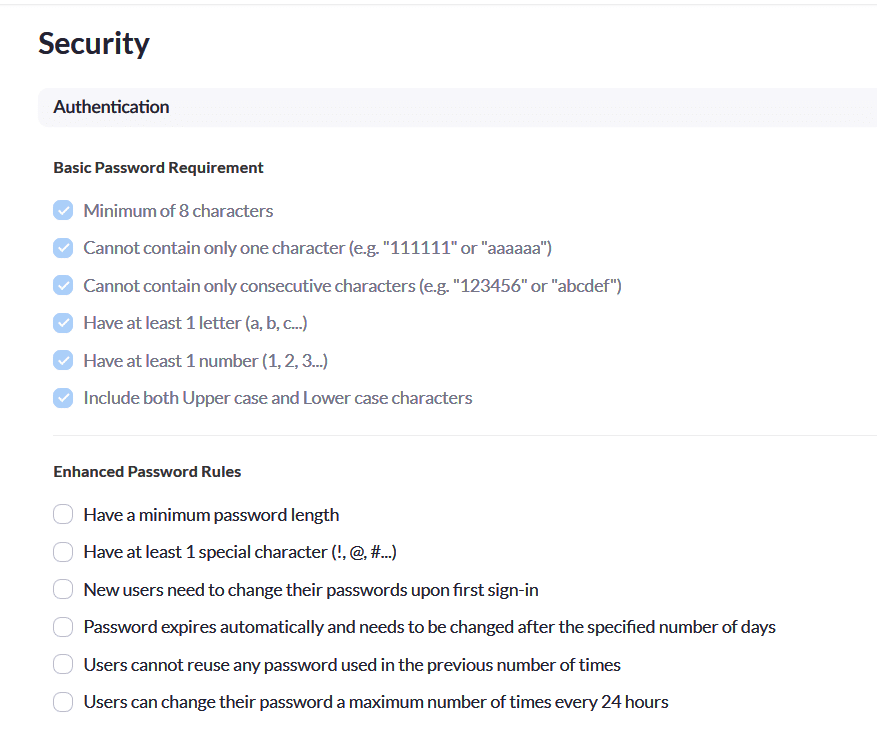
There is also a page where you can override password requirements for all users – handy if staff have not had time to be given training on how to use Zoom securely.
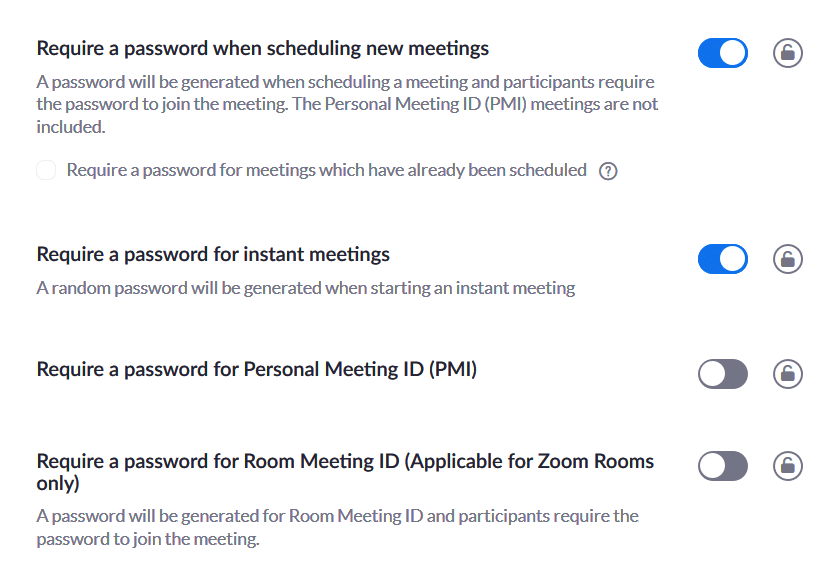
Finally – Hidden within the security options – are password features.
These can be enabled to match your password policy. https://zoom.us/account/setting/security
A final note on the Admin Account
As with any online software, the admin account represents the keys to the kingdom. Enabling 2FA and ensuring that account uses a strong password is key. As anyone with access to this account can download any recorded videos, add themselves to sessions and weaken the security of the entire system.
UPDATE (16th April) Since the release of this article, we’ve done some further testing and Zoom has rectified some of these issues. Video calls now require passwords and the host of the call must permit all guests by welcoming them through a digital ‘waiting room’. The same is said about calls made through phones.
Even though some of the above issues have been resolved, we would advise that you do not use Zoom as it still requires further tweaking to become a fully secure platform
