The Persistent Security Gaps In IoT Evolution
It’s no secret that IoT devices have become a fundamental part of our daily lives. Whether it’s the VoIP and AoIP systems that connect our calls, to the medical devices responsible for monitoring our health, to the industrial IoT (IIoT) machinery in factories, or the smart home systems that simplify household chores, IoT is everywhere. Here we are in 2024, we are witnessing rapid advancements in fields like artificial intelligence, large language models (LLMs), and quantum computing. Yet, despite this swift technological progress, the security of IoT devices disappointingly still lags behind.
Curiously, many IoT gadgets still suffer from old security weaknesses—those same issues we saw in tech from the 1990s, only now they’re hidden behind new complexities. Granted, there are a handful of IoT products out there built with solid security measures that make hacking a tough job, however, these well-protected devices are few and far between.
The IoT market is particularly delicate, both in terms of security and economics. It’s troubling to see that some products are specifically targeted towards buyers who aren’t very experienced with cybersecurity. And it’s not uncommon to find that even the manufacturers and vendors themselves skip out on implementing robust security practices.
In our research evaluations, especially during our Global Threat Assessments (GTAs)—where we dive deep into the cyber threats facing various sectors worldwide—we encounter a vast number of IoT devices. These assessments reveal a landscape where security is often an afterthought, a scenario that poses significant risks not just to individual users but across entire industries.
“The economics of IoT manufacturing drive device costs (and therefore component costs) to a minimum, often making security an expensive afterthought. Also, many of these devices are targeted at price-sensitive customers who lack experience selecting and deploying infrastructure securely.”
— Practical IoT Hacking: The Definitive Guide to Attacking the Internet of Things
During our Global Threat Assessments (GTAs), our work extends beyond merely analysing current cyber threats. We also devise new strategies to anticipate and counter potential attacks, tailored to the specific type of organisation or target. This includes gathering Open Source Intelligence (OSINT), exploring Dark Web activities, and simulating every conceivable action a malicious actor might undertake. In these assessments, we encounter a broad array of infrastructure components—not just IoT devices, but also Operational Technology (OTs), SCADA Systems, and even Industrial IoTs (IIoTs).

A Common Failure With IoT Security
It’s concerning to see how some companies, often unintentionally, set up their products for security failures from the get-go. For example, they might initially dispatch devices with preset, unchangeable login details like ‘demo:demo’ which is intended only for demo purposes, and when these devices eventually go live, these credentials often remain unchanged, making them an easy target for hackers looking to build or expand their networks of compromised devices, or “botnets”. Furthermore, some manufacturers opt for default passwords like ‘admin’ or ‘changeme’ and alarmingly, many users don’t bother changing these passwords. These passwords are often mentioned in the device’s user guide, practically inviting hackers to take control.

The Systemic Risks of IoT Device Exploitation
While the dangers of weak, common, or default passwords are well-documented, there is an even greater concern, one that affects not just individual devices but entire infrastructures. In our security research on IoT devices, we often focus on specific functions that have the potential to interact directly with the device’s system, thus posing a significant risk of exploitation.
Consider, for instance, functions that interact with system commands or layers, such as DNS settings or other network-related configurations. These functions might directly execute system commands based on inputs assumed to be harmless, such as an IP address, a DNS server address, or even a simple device name intended for network identification, however this information exposure can lead to vulnerabilities. If these inputs are manipulated maliciously, they can serve as a backdoor into the device.
This method of attack is not just theoretical but is currently effective against hundreds, if not thousands, of IoT devices! Once compromised, these devices can be harnessed by attackers to facilitate both external and internal attacks, impacting entire networks and the broader infrastructure connected to them. The capability for such expansive disruption underscores the critical need for robust security measures that go beyond simple password protection, addressing deeper systemic vulnerabilities within IoT devices.
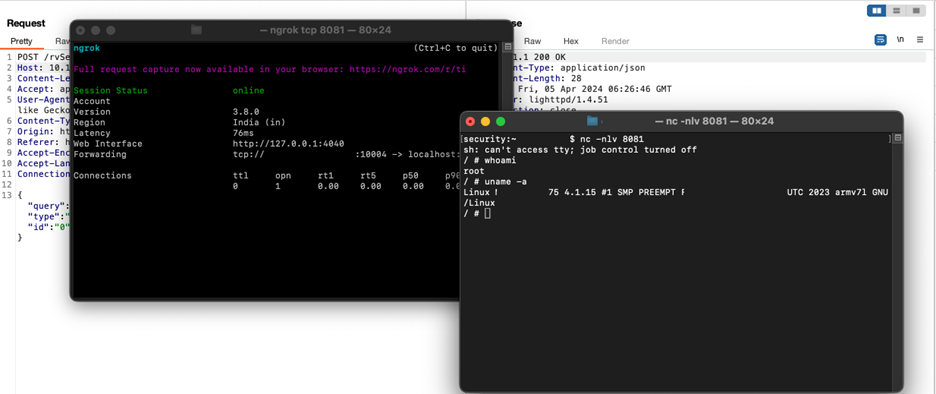
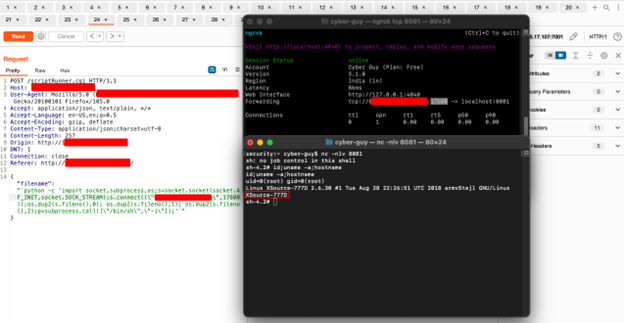
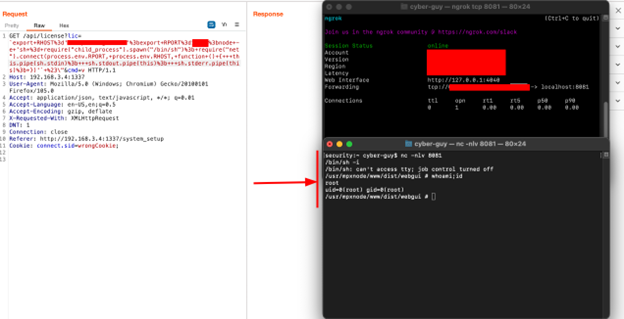
What you’re seeing above is not merely a series of exploits targeting the same device using different methods, or even exploits limited to a single manufacturer. The chilling reality is that the vulnerabilities depicted in these screenshots span a variety of products from multiple vendors; one device’s vulnerability lies in its license check functionality, another in how filenames are processed as system commands, and yet another through a system querying function. This function allows the device interface to directly interact with and query the system, potentially for executing commands or retrieving data. The vulnerabilities we’ve highlighted here are just the tip of the iceberg, and some major industry leaders are susceptible to these security flaws.
In the images above, every device depicted runs its applications with root privileges, a choice that underscores a common oversight in security for the sake of operational efficiency. Manufacturers will often prioritise immediate functionality and ease of use, enabling devices like AoIP and streaming media units to perform complex operations without permission barriers. This approach, while eliminating usability issues, neglects the vital aspect of security. Many manufacturers disregard the need for secure design principles because they focus primarily on cost efficiency.
This lack of security foresight means that once access is gained to such a device, the user—or in the case of a security breach, the attacker—gains complete control. This opens the door to severe threats, including ransomware, botnet creation, and other malicious activities, demonstrating a critical and widespread issue within IoT device security.

How Compromised IoT Devices Enable Widespread Network Vulnerabilities
When you consider the situation from a broader perspective, you’ll notice a common pattern among IoT developers, regardless of the programming languages they use. Whether it’s low-level languages like C/C++ or high-level languages like NodeJS, developers across the board often repeat the same security mistakes without realising the implications. This uniform oversight in diverse development environments highlights a significant lapse in awareness and security practices.
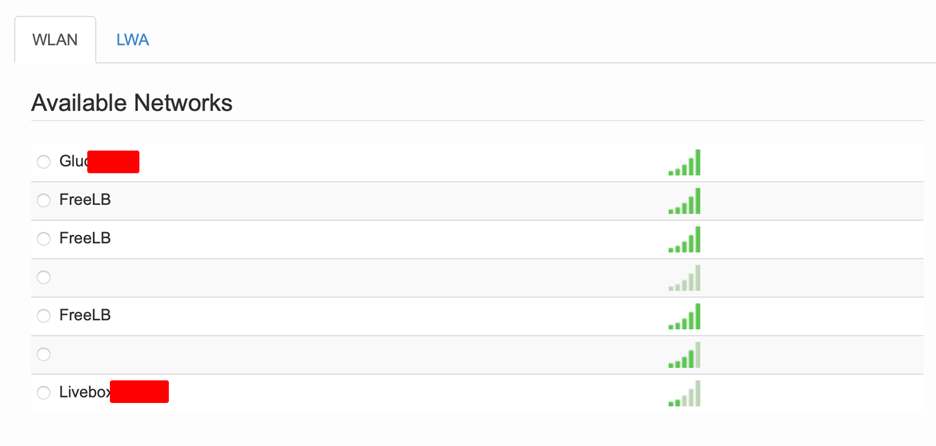
What manufacturers do not fully grasp is that their devices can act more as gateways—or “backdoors”—into larger systems, rather than merely functioning as independent units. Once an IoT device is compromised, it can serve as an initial beachhead for further incursions into a network, allowing attackers to move laterally and compromise additional systems. These devices could also be used to launch distributed denial-of-service (DDoS) attacks. Moreover, the inherent functionalities of these devices, such as the capability to generate radio frequencies, could be exploited for remote attacks or even transformed into tools for intercepting radio communications.
From an external perspective, these devices pose risks not just to the network they are directly connected to but also to surrounding devices, like Wi-Fi access points. We have already identified globally-used devices that are capable of launching attacks on Wi-Fi networks they are connected to, and guess what? These devices are also susceptible to OS Command Injection—a severe vulnerability that allows attackers to execute arbitrary commands on the device. This vulnerability can enable an attacker to go beyond breaching a single wireless network; it can gain access, take over its devices, and then use the compromised IoT device as a disguise to infiltrate and exploit other subsequent networks.
This domino effect of network vulnerability underscores the critical need for robust security measures in IoT devices, to prevent them from becoming unwitting tools in cyber attacks.
The risks of having exposed and vulnerable IoT devices are not just theoretical; they are a tangible, real, and pressing concern. In our assessments, we’ve encountered numerous devices that had been compromised, and many of these devices had already been manipulated to include backdoors, leaving them wide open to further exploitation.
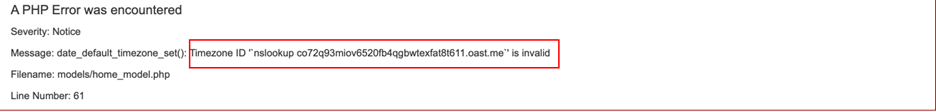
As you can see in the image above, the attacker specifically targeted a zero-day vulnerability, a previously unknown flaw, leaving clear evidence of the intrusion through detailed error messages. The device in question here is particularly significant—it’s an energy communication unit. So you can imagine the severity of this risk, as such devices, if compromised by state-sponsored attackers, could lead to devastating consequences for entire nations.

Key Takeaways
As we navigate the challenges posed by IoT devices, it becomes increasingly clear that both manufacturers and users play crucial roles in enhancing device security. Our research and analyses here highlights the need for a shift in how IoT security is approached, emphasising prevention over remediation.

Here are some of the key takeaways from our article:
- Security Gaps: Despite technological advancements, IoT devices still display vulnerabilities similar to those from the 1990s, now masked by newer complexities.
- Prioritising Speed Over Security: Many IoT devices are designed with cost reduction in mind, often at the expense of necessary security measures.
- Requirements for IoT Global Threat Assessments: These IOT assessments reveal widespread security neglect that threatens not just individual devices but entire infrastructures.
- Diverse Vulnerabilities: Security flaws span across different manufacturers and involve various methods of exploitation, including basic configuration errors and sophisticated system command injections.
- Need for Comprehensive Security Measures: There is an urgent requirement for manufacturers to integrate robust security at the design phase and for users to enhance their security practices.
Manufacturers must commit to embedding strong security features from the outset, while users must be educated and vigilant about their cybersecurity practices. Only through a concerted and collaborative effort can we hope to safeguard IOT devices, ensuring that the conveniences offered by these technologies do not come at the expense of our security and privacy.
